Ethical Hacker Methodology
Ethical Hacker processes and methodology, from enumeration to documentation

Ethical hacking, also known as penetration testing, is a controlled simulation of a cybersecurity attack with the intent of identifying weaknesses in a client's network security posture. Companies hire an ethical hacker to penetrate their network and test security practices, password policies, and even staff procedures. Afterward, the tester submits a report of all findings along with remediation steps for each issue. The goal is to strengthen overall security posture by identifying vulnerabilities before a malicious actor can exploit them.
An internal penetration test is done from inside the network. This usually means a VPN connection provided by the client or a laptop connected directly to the internal network by the penetration tester. Internal penetration tests simulate an attacker who has already breached the external perimeter and demonstrate what a malicious actor could do from inside the network.
Conversely, an external penetration test is done from outside the network. The ethical hacker simulates a remote attack, usually by first breaching some web application or login screen to gain a foothold into the internal network.
There is also a physical penetration test, in which the ethical hacker attempts to penetrate the physical building where the client operates. This is a great way to test the effectiveness of barriers like RFID scanners, fences, security cameras, and other external security controls.
The 5 Stages of Ethical Hacking
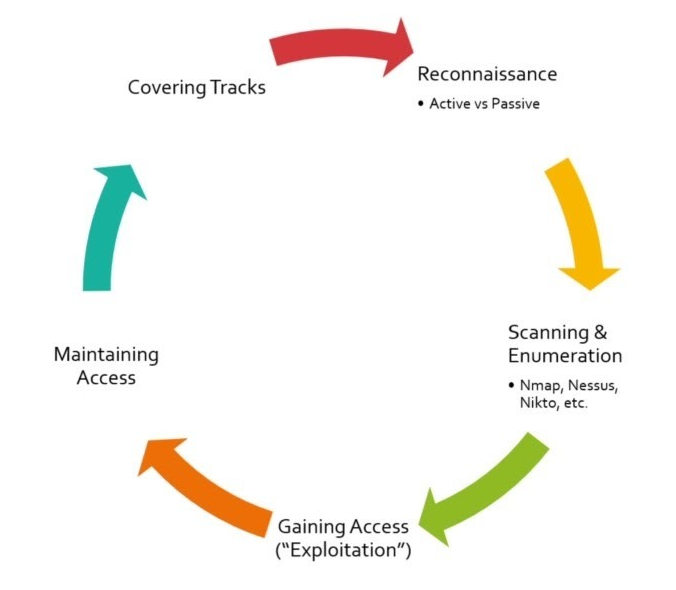
Stage 1: Reconnaissance
This stage is all about gathering information on the target to look for a foothold into the network. There are two types of reconnaissance: active and passive.
Passive reconnaissance involves using publicly available resources to gather as much information as possible, also called Open Source Intelligence (OSINT). Examples include social media sites like Twitter, Facebook, LinkedIn, Google searches, and WHOIS data when attacking a website. Look for company pages, employee Facebook pages, LinkedIn connections, or even an image posted by an employee showing their badge numbers. You can also look at nearby restaurants, food trucks, or anywhere employees gather during breaks. The key idea is that this is all passive, meaning there is no direct interaction with the target network.
Active reconnaissance involves interacting with the target network. Social engineering would also fit into this category.
Stage 2: Scanning & Enumeration
After gathering enough information on the client, it is time to scan the target network for open ports and protocols and check for known vulnerabilities that can be exploited. Tools like Nmap, Nessus, and Nikto fit into this stage. The goal is to find any way to gain remote code execution or some other form of access to the internal network.
Stage 3: Gaining Access ("Exploitation")
Once enough information has been gathered, the ethical hacker will run any previously identified exploits in an attempt to gain access. There are countless ways this can happen, such as SQL injection, remote code execution (RCE), cross-site scripting (XSS), or cracking login portals or password hashes discovered during the reconnaissance phase.
Stage 4: Maintain Access
After gaining access, it is important to establish some kind of persistence within the network. Passwords get changed, user accounts get added or removed, and systems get disconnected. It is important to ensure access can survive those changes.
If the cybersecurity team discovers that one of their accounts has been breached, disabling that account could effectively lock the tester out of the network. That means they may need to search for another vulnerability to exploit and regain access. Examples of persistence-related activity include backdoors, malware, rootkits, privilege escalation, or even adding new users under your control.
Stage 5: Covering Tracks
Once the assessment has been completed, this is the time to cover up or delete any indication that you were there. Remove any malware or rootkits that were installed, delete any logs or accounts that were created, and essentially return the network to the way it was when you started.
Ethical hackers are valuable for any business with sensitive information across networked computers. Whether it is a Fortune 500 company or a small therapy practice, ethical hackers can help organizations comply with industry standards, maintain HIPAA compliance, protect private information, and stay current with newly discovered vulnerabilities and exploits.
After the penetration test, it is important to get retested after about 90 days to give the company time to fix the findings. This second test helps confirm that vulnerabilities have been patched, security practices and procedures have been updated, and the overall security posture has improved.
Ethical hacking is a great way to test how employees, security policies, password policies, and other network security procedures will hold up against a malicious attacker. A penetration test is almost like a vaccine, providing a small dose of a malicious network attack to help strengthen the organization's overall security posture.
