My PNPT Experience
Training materials and exam experience for TCM Security's PNPT certification exam

Overview
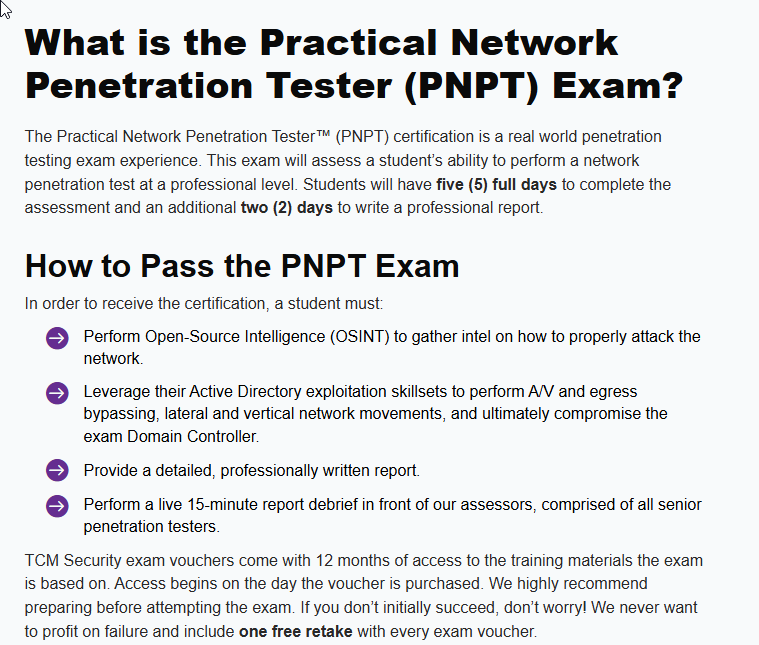
Recently, I took and passed the Practical Network Penetration Tester (PNPT) certification exam from TCM Security, which is sort of the next level up from the PJPT. The PNPT is an intermediate-level ethical hacking certification that tests your skills in Active Directory, OSINT, login brute forcing, password guessing, lateral movement, pivoting, and privilege escalation.
The $499 price is hefty, but still low for a professional certification. Included in that price tag is one free retake valid for a lifetime as well as almost 50 hours of training material with 12 months of access.
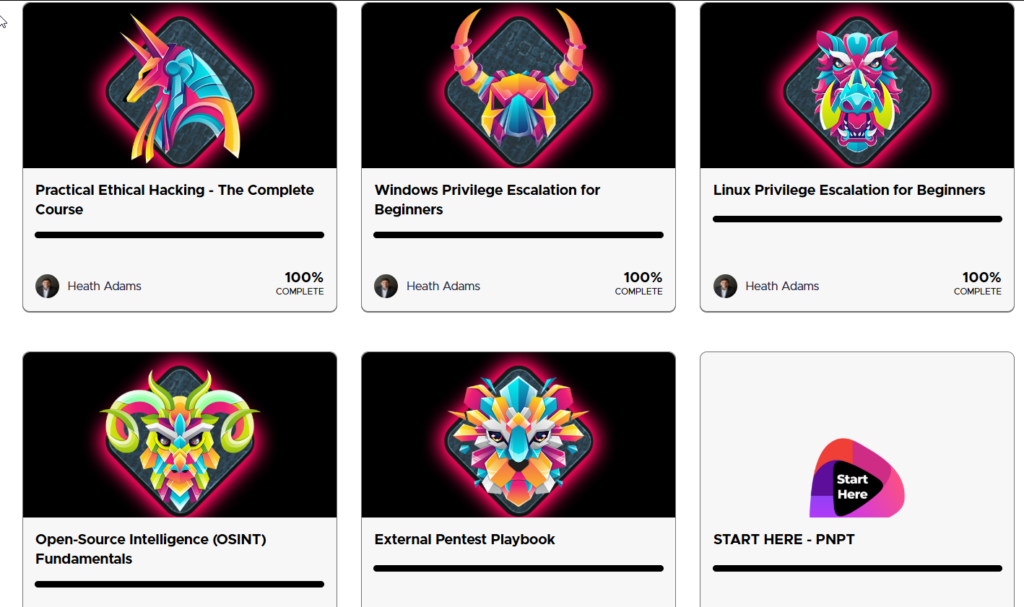
The PNPT bundle includes 5 courses total with clear, concise, step-by-step instructional videos that are easy to follow for some hands-on experience. The courses include:
1. Practical Ethical Hacking - The Complete Course2. External Pentest Playbook
3. OSINT Fundamentals
4. Windows Privilege Escalation
5. Linux Privilege Escalation
The Practical Ethical Hacking (PEH) course is the same PEH course from the PJPT, so I had a bit of an advantage in that I only had 4 more courses to make it through. I think there are also some free courses included with TCM Academy, including a course on soft skills for the job market that goes over resume tips, interviewing strategies, and some other non-technical skills to help land a pentesting role.
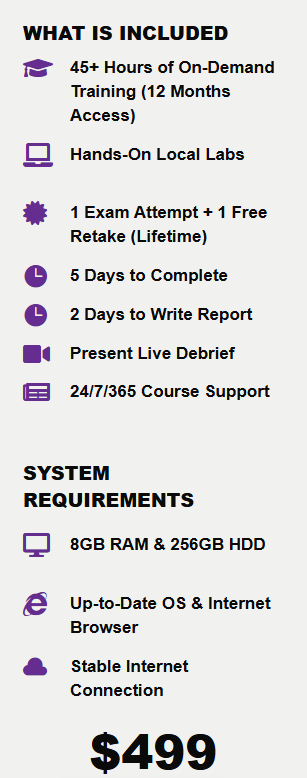
Unlike the PJPT, which does not expire, this certification expires 3 years from the certification date. Once you begin the exam, you have 5 days to fully compromise an Active Directory domain, plus an additional 2 days to write a professional pentest report. After that, you will have a 15 minute live debrief with TCM staff on camera where you present your results.
Training Materials
The PNPT includes 5 different courses for study material. Each course includes several hours of clear instructional videos to follow along with, as well as capstone exercises that test the skills learned in the course.
1. Practical Ethical Hacking - The Complete Course
This is the same PEH course used for the PJPT. It provides a broad overview of ethical hacking skills and methodologies, from basic bind shells and reverse shells to Active Directory enumeration and attacks, post-exploitation, and basic web application vulnerabilities.
One thing I love about this course is its use of hands-on study materials. After the non-Active Directory portion, there are about 5 vulnerable virtual machines complete with walkthroughs from the initial foothold to full root access. The Active Directory portion starts with a walkthrough for setting up an AD home lab with a domain controller and two workstations so you can follow along with the videos. The web application portion also includes a local web server to test vulnerabilities, along with walkthroughs for each attack. It is a very thorough course and I would recommend it to any aspiring hacker.
2. External Pentest Playbook
This course teaches you how to attack a network from the outside rather than starting from within the target subnet. While there is not as much hands-on lab work in this course, it provides a lot of valuable information on password guessing and discovery techniques, attacking login portals, privilege escalation, report writing, and common pentest findings. This course was very helpful for the exam.
3. OSINT Fundamentals
As the name suggests, this course covers the fundamentals of open source intelligence gathering. Whether you are looking for information on a business, image, email address, username, website, password, or person, this course provides a ton of resources for gathering the information you need. It also covers the intelligence lifecycle, OSINT automation, and OSINT report writing, and wraps up with some fun OSINT challenges.
4. Windows Privilege Escalation
This course covers a broad range of privilege escalation techniques for Windows. Some of the escalation paths include DLL hijacking, kernel exploits, password mining, port forwarding, RunAs, service permissions, startup applications, getsystem, executable abuse, registry abuse, impersonation, and potato attacks. The course also includes access to a Windows PrivEsc room on TryHackMe so you can follow along and try each technique yourself.
5. Linux Privilege Escalation
As you might expect, this course covers privilege escalation techniques for Linux. Some of the escalation paths include capabilities, Docker, NFS root squashing, SUID escalation, kernel exploits, scheduled tasks, sudo exploits, and some automated tools for privilege escalation and exploitation.
Exam
The PNPT exam was a lot of fun and a lot of frustration.
You have 5 days to attack and fully compromise an Active Directory domain from outside of the network, starting with an OSINT investigation to discover a way into the internal network. The exam tests your ability to brute force using Burp Suite, apply password guessing techniques from the course material, pivot using tools like sshuttle or proxychains, and perform Active Directory enumeration and attacks, all while thinking critically and paying close attention to detail.
To be completely open and honest, I failed the exam 3 times, all because I was thinking way too hard about it. I failed the first attempt without breaching a single account. That was rough. On the second attempt, I managed to breach the external network and set up a tunnel, but I made some bad assumptions about usernames. I got access to the internal network and moved laterally, but then got stuck on a particular machine. That same sticking point caused my second and third failures, and on the third attempt I gave up halfway through because I was so frustrated.
Fortunately, TCM offers additional retakes for $100, so you do not have to break the bank to keep trying. Their attitude of not wanting to profit from failure is honestly one of my favorite things about how they handle the certification.
What makes this exam great is that it is designed to mimic a real-world penetration test with absolutely no flags to capture. The course material repeatedly reminds you to think of it like a real pentest rather than a CTF, which I completely agree with. Enumeration is key here. If you are stuck, enumerate, enumerate, enumerate.
The exam is not proctored, but after 5 days the environment closes. Once I finally figured it out, I realized I was only about 10 minutes away from compromising the entire domain. I was so focused on what I thought should be there that I was overlooking what I had actually found.
Aside from the frustration, this was a lot of fun.
Tips & Tricks
The exam is not artificially difficult, but it can absolutely be frustrating. Once you finally compromise the domain controller, though, the feeling is worth every metaphorical hair pulled from your head. I made way too many assumptions and forgot the actual course material, which means I was thinking way too hard about certain parts of the process.
Here are my biggest tips for setting yourself up for success:
- Get plenty of sleep the night before your exam and eat something the morning of.
- Take as many breaks as you need. It feels counterintuitive, but stepping away from your computer can help you see the problem more clearly.
- Everything you need is in the course materials, especially PEH, External Pentest Playbook, and OSINT Fundamentals.
- Read everything you find in detail. Look through every file and folder you can access.
- Think of it like a real penetration test rather than a CTF or test question.
- The exam is not artificially difficult, but it is challenging.
- Check out the TryHackMe rooms Wreath and Holo to get a feel for what the exam is like.
- When writing the report, make sure you have a screenshot of every single step toward compromise.
- If you get stuck, take a break and look carefully at the information you already have. For any credentials you find, ask yourself what those credentials can access.
- Again, everything you need to pass the exam is in the course material.
Good luck, and happy hacking!

